Every device connected to a network laptops, smartphones, servers, tablets — represents a potential entry point for attackers.
These devices, known as endpoints, are often the weakest link in cybersecurity. A single compromised device can give attackers access to an entire network.
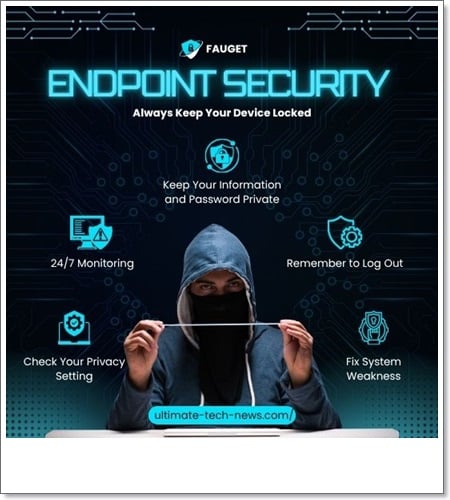
This is why endpoint security has become one of the most critical areas of modern cybersecurity.
Instead of focusing only on network protection, endpoint security ensures that every connected device is monitored, protected, and controlled.
In this guide, you’ll learn what endpoint security is, how it works, its components, benefits, and how to implement it effectively.
What Is Endpoint Security?
Endpoint security refers to the process of securing devices that connect to a network from cyber threats.
These endpoints include:
- Laptops and desktops
- Mobile devices
- Servers
- IoT devices
Endpoint security solutions monitor and protect these devices from malware, unauthorized access, and other cyber threats.
For technical reference, see this endpoint security guide
Simple Explanation
If your network is a building, endpoints are the doors and windows.
Endpoint security ensures that every door and window is locked, monitored, and protected.
Why Endpoint Security Is Important
Cyber attacks increasingly target endpoints because they are easier to exploit than centralized systems.
1. Increased Remote Work
More devices connect from outside secure networks.
2. Multiple Attack Vectors
Endpoints can be attacked through email, downloads, or web browsing.
3. Data Protection
Sensitive data is often stored on endpoint devices.
4. Preventing Lateral Movement
Stopping attackers from spreading within the network.
Without endpoint security, even strong network defenses can be bypassed.
How Endpoint Security Works
Endpoint security combines multiple technologies to protect devices.
1. Threat Detection
Identifies malicious activity on devices.
2. Real-Time Monitoring
Tracks endpoint behavior continuously.
3. Access Control
Restricts unauthorized access.
4. Response and Remediation
Blocks threats and restores affected systems.
These processes ensure that endpoints remain secure at all times.
Key Components of Endpoint Security
Antivirus and Anti-Malware
Detects and removes malicious software.
Endpoint Detection and Response (EDR)
Provides advanced threat detection and response capabilities.
Firewall Protection
Controls incoming and outgoing traffic on devices.
Data Encryption
Protects sensitive information stored on devices.
Patch Management
Keeps systems updated to fix vulnerabilities.
These components work together to provide layered protection.
Endpoint Security vs Network Security
Both are essential but focus on different areas.
- Network Security: Protects the network infrastructure
- Endpoint Security: Protects individual devices
For example, network monitoring tracks traffic, while endpoint security protects the device itself. Learn more in our network monitoring guide
Types of Endpoint Security Solutions
Traditional Antivirus
Basic protection against known threats.
EDR Solutions
Advanced detection and response capabilities.
XDR Platforms
Extended detection across multiple systems.
Mobile Device Management (MDM)
Controls and secures mobile devices.
Modern organizations often use a combination of these solutions.
Benefits of Endpoint Security
Improved Threat Protection
Detects and blocks attacks early.
Better Visibility
Provides insights into device activity.
Reduced Risk
Minimizes vulnerabilities.
Regulatory Compliance
Helps meet security standards.
These benefits make endpoint security essential for modern organizations.
Common Endpoint Security Threats
- Malware and ransomware
- Phishing attacks
- Unauthorized access
- Data breaches
Endpoints are often targeted because they are easier to exploit.
Challenges in Endpoint Security
- Managing multiple devices
- Keeping systems updated
- Detecting advanced threats
- Balancing security and usability
These challenges require a well-planned security strategy.
Best Practices for Endpoint Security
Keep Software Updated
Patch vulnerabilities regularly.
Use Strong Authentication
Enable multi-factor authentication.
Encrypt Sensitive Data
Protect data from unauthorized access.
Monitor Endpoint Activity
Detect suspicious behavior early.
Train Users
Educate employees about security risks.
Following these practices significantly improves security.
Future of Endpoint Security
Endpoint security is evolving with new technologies.
- AI-based threat detection
- Behavioral analytics
- Cloud-based security solutions
- Integration with SIEM and XDR
These advancements will make endpoint protection more effective.
Conclusion
Endpoint security is a critical part of modern cybersecurity.
It protects devices, prevents attacks, and ensures data security.
As cyber threats continue to evolve, securing endpoints is no longer optional — it is essential.
Strong endpoint security helps build a resilient and secure digital environment.
Frequently Asked Questions
What is endpoint security?
It is the protection of devices connected to a network.
Why is endpoint security important?
It prevents attacks targeting individual devices.
What is EDR?
Endpoint Detection and Response, an advanced security solution.
Is endpoint security necessary for small businesses?
Yes, all organizations need endpoint protection.
How is endpoint security different from antivirus?
Endpoint security includes antivirus plus advanced protection features.
Call to Action
Secure your devices today with strong endpoint security practices to protect your network, data, and users from modern cyber threats.