Cybersecurity is not just about preventing attacks — it’s about detecting them early, understanding them clearly, and responding quickly.
The challenge is that modern networks generate massive amounts of data. Logs from servers, applications, firewalls, and user activity all create noise. Hidden within that noise could be a real attack.
This is where SIEM becomes essential.
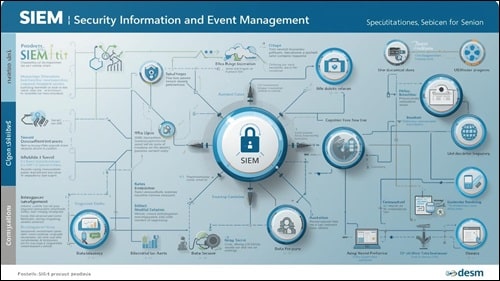
Security Information and Event Management (SIEM) helps organizations collect, analyze, and respond to security events in one centralized system.
In this guide, you’ll learn what SIEM is, how it works, its components, benefits, challenges, and why it is a critical part of modern cybersecurity.
What Is SIEM?
SIEM (Security Information and Event Management) is a cybersecurity solution that collects and analyzes security data from across an organization’s IT infrastructure.
It combines two key functions:
- SIM (Security Information Management): Collects and stores log data
- SEM (Security Event Management): Monitors and analyzes events in real time
Together, they provide a complete view of security activity across systems.
For a technical overview, refer to this SIEM guide
Simple Explanation
Think of SIEM as a central control room for cybersecurity.
Instead of checking each system individually, SIEM gathers everything in one place and tells you when something is wrong.
Why SIEM Is Important
Modern cyber threats are complex and often go unnoticed without proper visibility.
1. Centralized Visibility
All security data is collected in one place.
2. Faster Threat Detection
Identify suspicious activity in real time.
3. Improved Incident Response
Respond quickly to minimize damage.
4. Compliance and Reporting
Helps meet regulatory requirements.
5. Threat Correlation
Connects events across systems to detect advanced attacks.
Without SIEM, many threats remain hidden until it’s too late.
How SIEM Works
SIEM systems follow a structured process to detect threats.
1. Data Collection
Logs are collected from multiple sources:
- Servers
- Firewalls
- Applications
- Network devices
2. Data Normalization
Different log formats are standardized for analysis.
3. Correlation
SIEM identifies patterns across multiple events.
4. Alerting
Triggers alerts when suspicious activity is detected.
5. Analysis and Response
Security teams investigate and take action.
This process enables real-time threat detection and response.
Key Components of SIEM
Log Management
Stores and organizes large volumes of data.
Event Correlation Engine
Detects relationships between events.
Alerting System
Notifies security teams of threats.
Dashboard and Reporting
Provides visual insights and reports.
Threat Intelligence Integration
Uses external data to identify new threats.
These components work together to provide a complete security solution.
SIEM vs Traditional Monitoring
Traditional monitoring focuses on performance, while SIEM focuses on security.
- Monitoring: Tracks system health
- SIEM: Detects and analyzes threats
For example, network monitoring shows traffic patterns, while SIEM analyzes those patterns for potential attacks. Learn more in our network monitoring guide
Use Cases of SIEM
Threat Detection
Identify malicious activity.
Incident Investigation
Analyze past events to understand attacks.
User Behavior Analysis
Detect insider threats.
Compliance Reporting
Generate audit logs and reports.
These use cases highlight SIEM’s importance in modern security environments.
Benefits of SIEM
Improved Visibility
Centralized view of security events.
Faster Detection
Identify threats quickly.
Better Decision Making
Data-driven insights.
Enhanced Security Posture
Stronger overall protection.
These benefits make SIEM essential for organizations handling sensitive data.
Challenges of SIEM
- High implementation cost
- Complex configuration
- Handling large data volumes
- False positives
Proper setup and management are crucial for success.
Best Practices for SIEM Implementation
Define Clear Objectives
Understand what you want to achieve.
Integrate All Data Sources
Ensure complete visibility.
Regularly Update Rules
Adapt to new threats.
Train Security Teams
Ensure effective use of SIEM tools.
Monitor and Optimize
Continuously improve performance.
These practices help maximize SIEM effectiveness.
Future of SIEM
SIEM is evolving with new technologies.
- AI-driven analytics
- Automated response systems
- Cloud-based SIEM solutions
- Integration with XDR platforms
These advancements will make SIEM more powerful and efficient.
Conclusion
SIEM is a critical component of modern cybersecurity.
It provides visibility, detects threats, and enables faster response.
Without SIEM, organizations struggle to manage complex security environments effectively.
If you want advanced protection, SIEM is not optional — it is essential.
Frequently Asked Questions
What does SIEM stand for?
Security Information and Event Management.
Is SIEM only for large organizations?
No, smaller businesses can also benefit.
Does SIEM prevent attacks?
It detects and helps respond but does not directly block attacks.
Is SIEM difficult to use?
It can be complex but becomes easier with proper training.
How is SIEM different from IDS?
IDS detects threats, while SIEM analyzes and correlates multiple events.
Call to Action
Take your cybersecurity to the next level by implementing SIEM and gaining complete visibility into your security environment.